View system configuration and FTP activity
Administrators can use the System Audit History page to track all system configuration and FTP activities, ordered by the most recent events.
Tracked events
These events include changes in the following:
-
user preferences
-
user profiles
-
data visibility profiles
-
FTP activity
-
search exports
-
exporting data model, user list, reference data, reference aliases
-
custom tables (reporting)
-
subscription jobs
-
configuration activities that require adding or changing system settings
View audit log
-
In the Admin console, click in Logs > System Audit History.
By default, up to 50 entries for the past day display.
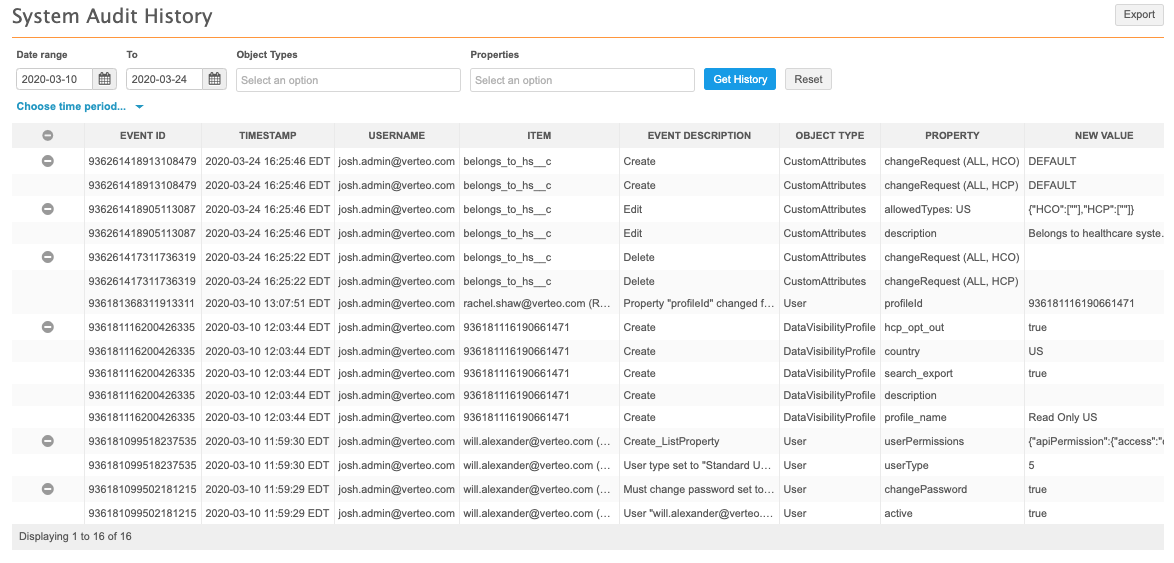
Each series of events is grouped according to Event ID. You can collapse a group by clicking its ![]() icon. Expand the group by clicking the
icon. Expand the group by clicking the ![]() icon.
icon.
View events
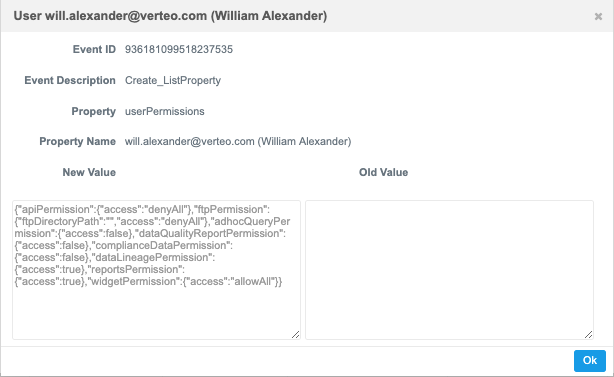
Click any event line to view the specific details of the event, including the event description, property affected, new value, and old value, if applicable.
Event details
Each event includes the following information:
- Event ID - a unique ID for each group of related events.
- Timestamp - the date stamp for the system event.
- User Name - the initiator of the event or
System. - Item - the specific target of the event; for example, a Network field name, user, configuration ID, or entity ID.
- Event Description - the type of event that occurred. This could be a detailed description of the event or any of the following:
 Possible values
Possible valuesAnonymize: an event used to anonymize data; for example, audit logs.Clone: an event used to clone a subscription.Create: an event that adds a property value that didn't previously exist.Create_ListProperty: an event used to add certain user settings.Delete: an event that removes a property value.DeleteAdHocJob: an event used to delete an ad hoc job file.Download: an event used to download a file from File Explorer.DownloadAdhocInput: an event used to download an ad hoc match input file.DownloadAdhocResult: an event used to download an ad hoc match result file.DownloadFromOpenData: an event used to download a record from Veeva OpenData.DownloadReportResult: an event used to download report results.Edit: an event that changes a property value.Edit_ListProperty: an event used to update certain user settings.InboxExport: an event used to export Inbox tasks.Remove File: an event used to remove a subscription export file.Renaming: an event used to rename a file or folder.RunReport: an event that runs a report.SearchExport: a search results export event.Start: an event used to start a subscription job or a DCR Cleanup operation.SyncWithOpenData: an event used to synchronize a record with Veeva OpenData.Upload: an event used to upload a file to File Explorer.Upload File: an event used to upload a subscription export file.UserPreferences: an event used to update the Inbox layout.UserReset: an event used to reset the Inbox layout. - Object Type - the type of object affected by the event, corresponding to a property or set of properties on a page in Network. This could be a detailed description of the event or any of the following:
 Possible values
Possible valuesAuditLogConfiguration: a setting for data retention.Canvas: an edit operation on the Network Explorer canvas.ConcurSettings: a Concur integration configuration.CustomAttributes: a custom field.CustomKeys: a custom key.DACRules: a rule for dynamic access control.DataQualityReport: a Network data quality report.DataVisibilityProfile: a Network data visibility profile.DCRCleanup: an operation to bulk approve, reject, or cancel add or change requests.DownloadFromOpenData: the complementary object for theDownloadFromOpenDataevent.EmbeddedNetworkWidget: a Network widget.ExternalCredential: credentials for an external non-Network service.FileSystemExplorer: an FTP-related operation within Network.FTPOperation: an FTP-related operation.GeneralSetting: a feature on the General Settings page.Group: a Network user group.Instance: a Network instance.JobValidationRule: a job validation rule.MatchConfigCountryGroup: a country group match configuration.MergeRule: a merge rule configuration.ObjectTypeInfo: a custom object.PermissionSet: application-level access to features.PasswordPolicy: a security policy for user profiles.ReferenceCode: a Network reference code.ReferenceGroup: a group used for reference data mappings.ReferenceValue: a reference value.Report: a Network report.ReportingCustomFolder: a folder created for private or shared custom tables in the SQL Query Editor.ReportingCustomTable: a custom table in the SQL Query Editor.ResolutionNotes: a resolution note on a change request.SearchExport: a search results export operation.SourceAlias: the source alias for reference data mappings.SsoSetting: a setting for single sign-on configuration.Subscription: a Network subscription.SubscriptionGroup: a group of OpenData countries.SubscriptionMatchConfig: a subscription match configuration.SubscriptionRule: a Network expression rule for a subscription.SubscriptionSchedule: a Network subscription schedule.SyncWithOpenData: the complementary object for theSyncWithOpenDataevent.System: a system for use with subscriptions or integrations.TargetAlias: the target alias for reference data mappings.User: a Network user profile.UserExport: the user account list download.UserGroup: a user management feature for users.UserPreferences: Inbox layout preferences.VeevaOpenDataBridge: a connection to Veeva OpenData.WorkflowSettings: the Network workflow configuration. - Property - the object property that was changed. The values for this property can vary: it might represent a specific property or value in the Network UI; for example, locale or first name for a Network user profile, a status flag, an Inbox or profile layout, or a label. The context of the property relative to the corresponding object type, event, and values will help in determining its function.
- New Value - the value assigned to the new or changed object property.
- Old Value - the previous value assigned to an updated object property.
Tip: User Name, Item, Property, New Value, and Old Value columns - If the content in the column is too long, hover over the cell to display a tooltip containing the full text.
The possible values listed here include the most common values for each column. If you don't see the definition for a value that appears in an audit history log in your instance, let us know.
Filter by date
To view results for a specific time period, perform one of the following actions:
-
Date range - Define a date in the Date range and To fields.
-
Time period - Expand the time period list and select a predefined period, for example, Last 7 days.
The Last day option can display up to two days of results, including the data from the previous day through to the current time.
Click the Get History button to view the results.
Filter by object type and property
Use the Object Types and Properties filters at the top of the history to refine the audit history by a specific object and its corresponding properties. The Object Types list is populated by a preset list of Network system audit objects; the Properties list is populated by all properties available for the specified object types.
Click a drop down list, select one or more values from the list, and click the Get History button to refine the history. You can click the Reset button to start over.
Note: You can select one value from the Properties drop down list, and multiple values from the Object Types drop down list.
Export the audit history
To download the refined audit history to your local file system, click Export.
The log is downloaded as a .csv file that you can open using a spreadsheet application.
FTP Activity
The following FTP user activities generate logs:
- logging in
- oploading files
- uploading folders with files
- renaming files and folders
- moving files and folders
- uploading folders or files with insufficient permission
- creating a new file with insufficient permission
- deleting a file with insufficient permission
- confirming that third party data is being loaded
Relevant activities are logged for auditing and can be downloaded in the .csv file.